Financial Services & Neo4j: Cybersecurity

Vice President, Product Marketing
4 min read

Cybersecurity is of critical importance to financial services firms.
IT organizations must mitigate cybersecurity risk, both in terms of external access to the infrastructure and in understanding how a malware infection or attack can move across a particular network.
These efforts are made challenging by the complexity of the data center. Between thousands of servers and a web of physical and virtual networks, IT professionals in the financial services sector need a technology that maps and visualizes this data effortlessly in order to effectively mitigate cybersecurity attacks.
In this series on Neo4j and financial services, we’ll be looking at how today’s finance enterprises are effectively solving emerging challenges in the industry. In previous weeks, we’ve taken a closer look at financial asset graphs, data lineage, metadata management, fraud detection, anti-money laundering (AML), network and IT infrastructure monitoring and identity and access management.
This week, we’ll take a closer look at cybersecurity.
Graph Technology for Cybersecurity
A typical bank will have tens of thousands of Linux, Windows and other servers as well as hundreds of thousands of desktops. Everything is connected to everything else across many physical and virtual networks and subnets.
In order to implement the proper controls and shore up exposed assets, IT must have visibility across the entire infrastructure. IT must know which customers and which employees are accessing what pieces of the infrastructure and what resources are made available to them. IT must also track which systems are connected.
Using a graph data model, cybersecurity experts no longer have to think of cyberattacks in
terms of discrete tables, lists and logs, but instead can track attacks (or potential attacks)
more intuitively across their entire IT infrastructure.
Neo4j can be used to identify single points of failure within a network before the vulnerability is known to attackers, and real-time, connected data queries can quickly alert cybersecurity experts if typical attack patterns are occurring within a network, even if individual data points don’t appear to be malicious.
By strengthening cybersecurity across a financial services firm, Neo4j keeps business running as usual while protecting mission-critical systems from would-be criminals.
Case Study: MITRE Corporation
In their efforts to stop cyberattacks, analysts track large amounts of detailed information, such as network and endpoint vulnerabilities, firewall configurations and intrusion detection events.
The solutions they use to analyze this data typically track individual data points. But to be successful, analysts need to understand how data points are related.
To address these challenges, researchers at the MITRE Corporation, a U.S. federally funded, not-for-profit company, are developing a tool for cyberwarfare analytics, visualization and knowledge management.
CyGraph brings together isolated data and events into an ongoing overall picture for decision support and situational awareness. It prioritizes exposed vulnerabilities, mapped to potential threats, in the context of mission-critical assets. It also correlates intrusion alerts to known vulnerability paths and suggests the best course of action for
responding to attacks.
For post-attack forensics, CyGraph shows vulnerable paths that warrant deeper inspection.
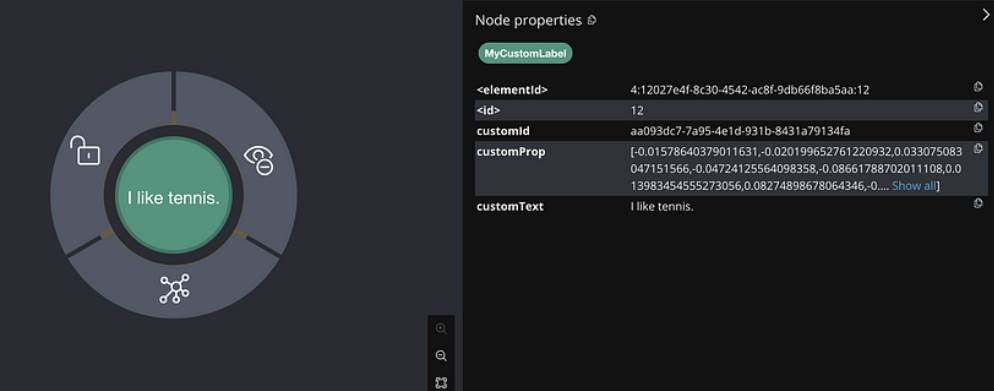
Rather than being fixed, the model schema in the CyGraph architecture is free to evolve with the available data sources and desired analytics. The data model is based on a flexible property-graph formulation implemented in Neo4j. REST web services provide interfaces in CyGraph for data ingestion, analytics and graph visualization.
Data in the wild is mapped to the common CyGraph data model in a two-step process. Data is normalized and stored in a document-oriented database and then represented as a graph in Neo4j.
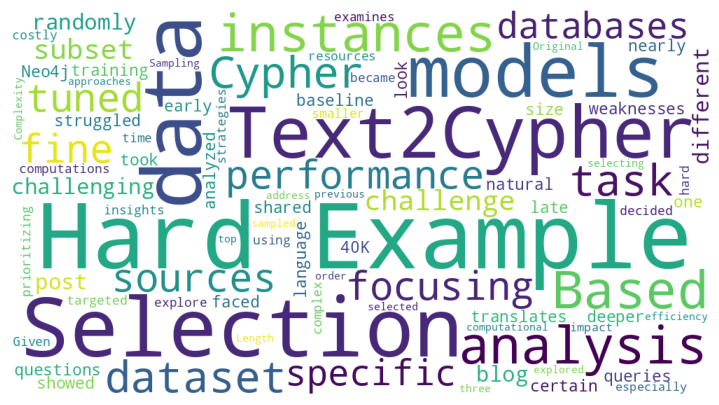
The Neo4j native graph pattern-matching language – Cypher – supports a library of domain-specific queries as well as flexible ad hoc queries. CyGraph then provides a variety of clients for specialized analytic and visual capabilities including graph dynamics, layering, grouping, filtering and hierarchical views.
The use of Neo4j at the MITRE Corporation provides insight into the mission impact of cyber activities. Graph layers (network infrastructure, cyber defensive posture and threats, mission dependencies and so on) define subsets of the overall model space with relationships within and across each layer. Analysts can also gain visibility into operations for global situational awareness.
Conclusion
Today’s cybersecurity threats are constantly evolving, and your IT organization needs a technology that evolves, not just alongside, but ahead of those threats. That solution is the Neo4j graph database.
Using Neo4j, your IT organization can easily map out every facet and firewall of the IT infrastructure at your financial services firm. Then, using dynamic Cypher queries, you can stay one step ahead of potential attackers, creating a sustainable competitive advantage for your organization.
In the coming weeks, we’ll take a closer look at other graph technology use cases within the financial services industry, including master data management and customer experience management.
Catch up with the rest of the financial services and Neo4j blog series: