Move AI from pilot to production: A fireside chat with Arhasi | Asia Pacific
Asia Pacific
Lower cost. Reduce risk. Inform decisions.
170+
Partner ecosystem
80+
Fortune 100 customers
300k
Developers building








Neo4j is acquiring GraphAware, our longtime partner and a leading provider of intelligence analysis software for government agencies.
Read moreNODES 2026: Call for Papers | Engineering Better Intelligence Sessions are educational and show how to solve a problem using code, data sets, or best practices. Deadline is June 15.
Submit a Talk230% ROI: IDC validated $4M in annual value and a 7.8-month payback for enterprises running Neo4j.
See the Results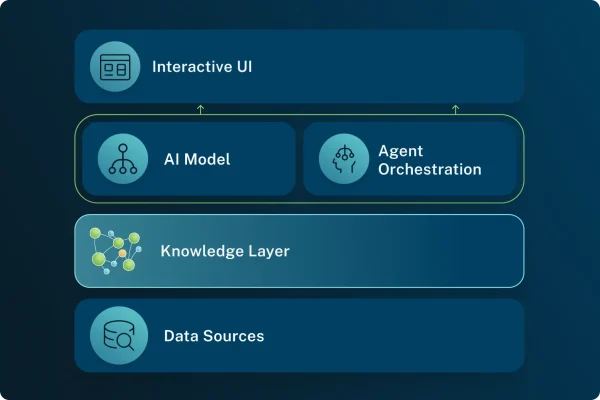
A knowledge layer provides the context, memory, and map of your data that your AI needs to make trustworthy decisions. It connects your essential enterprise knowledge to your AI and agentic systems, so that AI can understand the relationships, history, and decisions behind your business.
Get accurate, explainable, and complete data for AI with a knowledge graph.
Build with a comprehensive, easy-to-use, trusted database.
Build with a comprehensive, easy-to-use, trusted knowledge layer.
Secure, govern, and scale your graph with robust controls, encryption, and compliance across any cloud.
Graphs
Uptime SLA
Graph algorithms
Premium support
Retention backup
Tools and resources to start building graph-powered apps today.
Whether a beginner or an expert, level up your skills with our free courses.
Learn more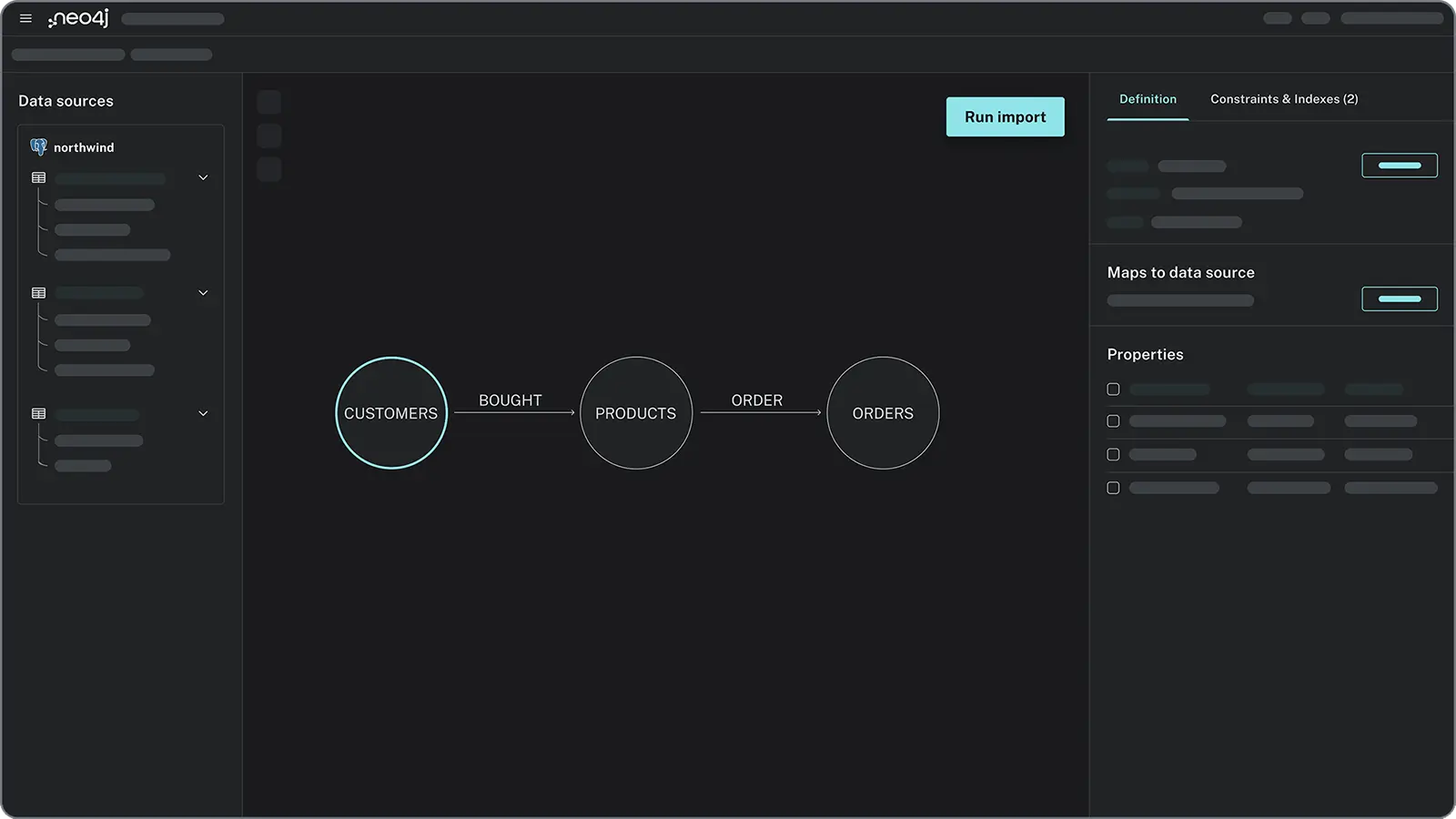
Easily import data from CSV, JSON, APIs, or integrations like Kafka and Spark. Use our intuitive tools to model your data as a graph, capturing entities and relationships without rigid schemas.
Use simple, intuitive queries with Cypher to find patterns in your data quickly — no more complicated JOINs or nested queries.
Visualize your data as graphs with our interactive tools. Spot patterns, refine queries, and explore relationships — no extra code required.