GraphConnect 2014 Sponsor, Linkurious, discuses mapping fraud with Neo4j
Originally posted on the Linkurious blogDrug lords are not the only persons using mules to launder money. eCommerce operations are confronted to “reshipping scams”. In these scams, mules are used by online fraudsters to turn their credit cards into actual goods. Graphs can help detect this fraud.
When a job ad turns you into a money laundering mule
We have already discussed about credit card fraud on this blog by addressing how credit cards get stolen. But do you know what happens next? If you have been frequenting the internet at any point during the past 10 years you may have come into contact with a job ad for a re-shipping position. Reshipping is used by fraudsters to launder the money from their stolen credit card.
It works like this :
- the criminals steal credit cards information ;
- they buy goods on ecommerce websites ;
- the goods are sent to a third party (the mule) ;
- the third party receives the goods and re-ships them to the criminal (hence the term reshipping);
- the criminal sells the goods and receives cash ;
The third party, recruited via a job ad promising a generous compensation, acts as mule. His role is twofold. First, the mule helps deceive the ecommerce website. If the fraudster was asking for a delivery in Ukraine or Nigeria, it would probably ring some bells. However if during his checkout he asks for his goods to be delivered to an address in the US, it will seem normal.
The second role of the mule is to isolate the fraudster from investigations. When the ecommerce website, the credit card provider or the credit card holder detect the fraudulent transaction, they will turn to the mule. The mule will have to prove that he/she did not steal the credit card in the first place. Meanwhile the fraudster will be safe and sound, enjoying his cash in another country.
The most sophisticated reshipping organizations work as white-label money laundering services. The US authorities are noticing this : they have severely cracked down on reshipping rings recently. The rationale behind this is simple : make it harder to launder money and the incentive to commit fraud will decrease. Soldiers like to talk about the “kill chain“, the series of stages involved in an attack. A defense only have to stop the attack at one stage of the kill-chain to be successful.
Money-laundering is the last stage in credit card fraud…and the last opportunity to act before it is too late. We are going to see how ecommerce websites can identify reshipping scams and save money.
Looking for suspicious patterns in online transactions
Let’s start by considering the information a ecommerce website may have. For any given order it stores (among other things) :
- an order ID ;
- various order information : date, content, total ;
- a billing address (composed of a street, a city and a country) ;
- a shipping address (composed of a street, a city and a country) ;
- an IP address (that can be geolocalized and is thus linked to a city and country) ;
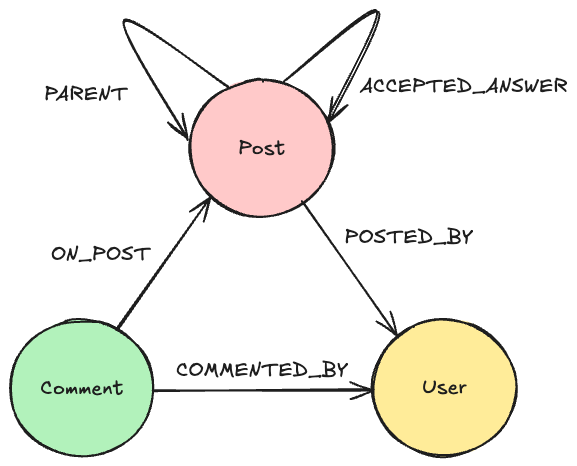
The information can be modeled as this :

There is a couple of things we can do with that data to identify fraud. A first step might be to compare the billing and shipping addresses. A difference between a billing and a shipping address might be indicative of a reshipping scam. Furthermore we can look into the IP address. If the IP address localization does not match the billing address or the shipping address, the situation is highly suspicious.
We are going to see how to perform these security checks with a graph database.
Concrete example
I have prepared a small dataset with a few (fake) ecommerce orders. It includes regular transactions and fraudulent transactions. The data has been loaded into a Neo4j graph database.
First of all, we are going to see the list of the transactions in our dataset. To do that we can type into the Neo4j console (or within Linkurious) :
|
MATCH (orders:Transaction)
RETURN DISTINCT orders.date as date, orders.items as items, orders.amount as amount
ORDER BY amount DESC
|
We have 5 results.
| date | items | amount |
|---|---|---|
| 11/08/2014 | Perfume | 99$ |
| 11/08/2014 | Laptop, gifcard | 878$ |
| 11/08/2014 | Mobile phone | 499$ |
| 11/08/2014 | Nike sneakers, Football jersey | 299$ |
| 11/08/2014 | A Wonderful World | 10$ |
Now we want to return all the transaction that have a different billing and shipping address addresses :
|
MATCH (address1:Address)-[IS_SHIPPING_ADDRESS]->(suspiciousorder:Transaction)<-[:IS_BILLING_ADDRESS]-(address2:Address)
WHERE address1 <> address2
RETURN DISTINCT suspiciousorder
|
We have 3 results : the $99, $499 and $878 transactions.
These transactions are suspicious and could be flagged as such for further investigation. Even more suspicious are the transactions where the IP address is coming from a location different of the other addresses. We can identify that pattern by typing the following query :
|
MATCH (a:Transaction)-[r*2..3]-(b:City)
WITH a, COUNT(DISTINCT b) AS group_size, COLLECT(DISTINCT b) AS cities
WHERE group_size > 2
RETURN a, cities
|
The alert brings our attention to an IP located in Lagos, Nigeria. This is a known hotbed for online fraud. The IP address is associated to two transactions. In both of these transactions, the billing address and the shipping address are different : this is indicative of a reshipping scam.
We can see this in the graph visualization below. The countries are in dark green, the cities in blue, the IP address in red, the street in orange, the orders (with their date) in light green and the addresses in asparagus.

Network visualization helps us understand the link between the 2 orders, the IP address in Nigeria, the address in Detroit and the credit card owners in San Francisco.
Network visualization allows us to turn the alert triggered by the detection pattern we wrote into something more. Now we know that our ecommerce operation is used by a scam artist in Nigeria who is using (unwilling?) accomplices in the US to launder his money. We can freeze any further transactions from the IP address and alert the authorities to investigate the US accomplices.
Of course the data we have used here is fake. Furthermore, the fraudsters could use more advanced techniques (starting with a simple proxy for example) to avoid detection. Nevertheless, the same approach (tweaked) of identifying fraudulent patterns and looking for them can be used successfully to fight against reshipping and ecommerce fraud.
Reshipping scams are used to launder money for various criminal activities. We have seen that ecommerce websites can use their data to identify potentially fraudulent transactions before it is too late.
GraphConnect 2014 SF
Linkurious will be a sponsor and panelist at GraphConnect 2014 SF. GraphConnect is the world’s only conference focused on the rapidly growing world of graph databases and applications. Join over 700 graphistas from around the world on October 22, 2014 at SFJAZZ in San Francisco to hear more from Linkurious, as well as from companies like UBS, eBay, ConocoPhillips, CrunchBase and more. Visit www.graphconnect.com to register and get more information.