
Welcome to this week in Neo4j where we round up what’s been happening in the world of graph databases in the last 7 days.
Featured Community Member: Mike Morley
This week’s featured community member is Mike Morley, President at Menome Technologies Inc, a Calgary based organisation whose mission is to help organisations fully realize the value of their data.

Mike Morley – This Week’s Featured Community Member
Mike has been part of the Neo4j community for the last couple of years and founded Menome Technologies, a company that has Neo4j at the core of its business.
Mike blogs regularly about his experiences with graph databases and organises the Calgary Neo4j meetup.
In this week’s online meetup Mike, Mark Barley, and Konrad Aust showed us the tools they’ve been building to help enterprises break down data silos and capture critical knowledge.
On behalf of the Neo4j community thanks for all your work Mike!
ICIJ release Paradise Papers version of Neo4j Database
Late last week The ICIJ released an ICIJ version of Neo4j Desktop which includes the Paradise Papers and the other Offshore Leaks graph data.

Neo4j Desktop for ICIJ
On the back of that my colleague Gerrit Meier has created sdn-paradise – a Spring Data Neo4j project that allows you to analyse the Paradise Papers.
Graph Powered Search with Elastic and Neo4j
Michael Hunger, Christophe Willemsen, and Alessandro Negro have created a DZone Graph Powered Search Refcard .

Graph-Powered Search: Neo4j & Elasticsearch
It includes code and examples for using Elasticsearch to enable full-text search and Neo4j to power graph-aided search.
Fraudsters, Terrorists, Knowledge Graphs, Jim Webber Interview
-
- Georg Heiler shows how to identify hidden fraudsters and terrorists using Neo4j by looking at their distance from known people. Georg’s code is also available as a Jupyter notebook.
- Rolf Håvard Blindheim’s django-chemtrails uses Neo4j to help determine if a user has permissions to perform some action on an object, based on the relationship between entities.
- Chun Li has created FindMyCar, a Flask application on top of a used cars knowledge graph. Chun also posted a video that explains how to use the system and shows the Cypher queries behind the application.
- Silicon Angle have an interview with my colleague Dr Jim Webber and Comcast’s Director of Engineering for IoT, Mark Hashimoto – Graph databases are hot, but can they break relational’s grip?. They talk about the use cases for which graphs are a good fit and the performance improvements they give over relational databases for certain workloads.
Cyber threat intelligence
We’ve previously covered the use of Neo4j for security and threat detection and this week I came across a tool in that ecosystem called StixToNeoDB.
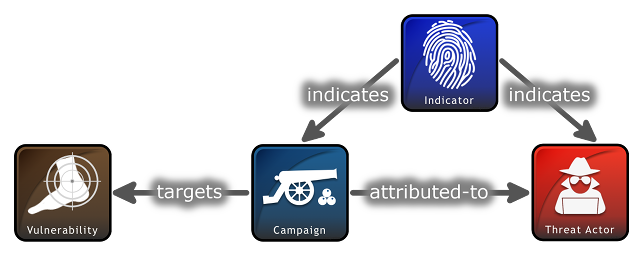
STIX – Sharing threat intelligence just got a lot easier
Structured Threat Information Expression (STIX) is a language and serialization format used to exchange cyber threat intelligence.
StixToNeoDB loads STIX objects and relations from JSON and zip files into Neo4j.
Tweet of the Week
My favourite tweet this week was by Charlene Tay:
Thanks! Yes, we really like Neo4j! Great work on the product 🙂 We’ve created our graph-based recommendation system and have had some good results so far.
— Charlene Tay (@charrtay) December 5, 2017
Don’t forget to RT if you liked it too.
That’s all for this week. Have a great weekend!
Cheers, Mark









