Neo4j Blog
Introducing AI-Powered Dashboard Creation in the Aura Console
We’re excited to announce a significant step forward for Neo4j AuraDB users: Dashboards, a powerful new tool in the Aura console.
6 min read


Everything a Developer Needs to Know About the Model Context Protocol (MCP)
25 min read
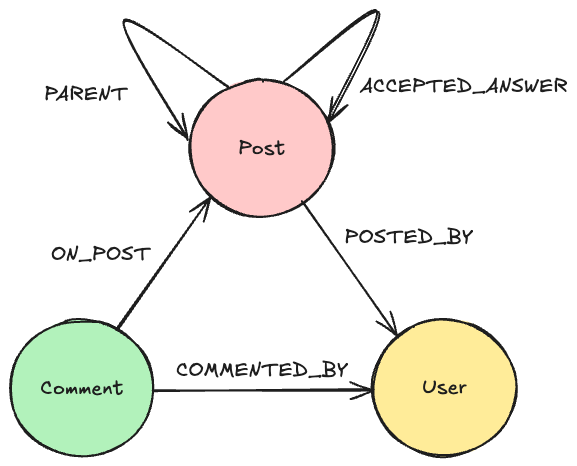
How to Improve Multi-Hop Reasoning With Knowledge Graphs and LLMs
9 min readFeatured Voices



Most Recent
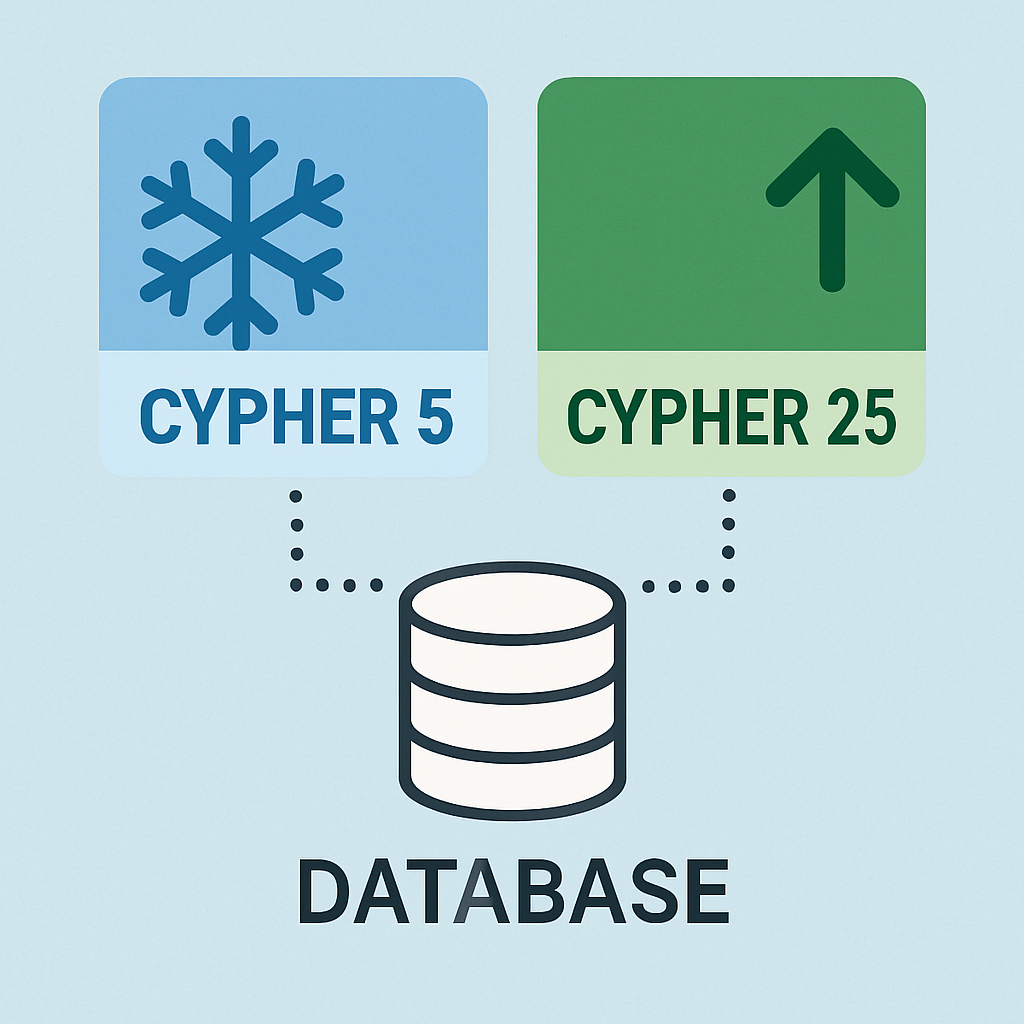







Integrating Neo4j With Symfony: Profiling Queries and Centralized Logging
4 min read
Neo4j Graph Analytics for Snowflake: Bringing Graph-Powered Insights to the AI Data Cloud
3 min read