Financial Services & Neo4j: Identity & Access Management

Vice President, Product Marketing
3 min read

Within the IT organization of any financial services enterprise, identity and entitlements management must be managed to minimize risk.
Over time, the centralized entitlements structure – whether represented in Active Directory or an LDAP directory – grows in such a way that people end up having more permissions than they need. As a result, your financial services firm is put at risk.
In order to reduce that risk and effectively manage your organization’s entitlement structure, you need a technology that is adept at tracking and adapting to a web of interconnected relationships. That is, graph technology.
In this series on Neo4j and financial services, we’ll be looking at how today’s finance enterprises are effectively solving emerging challenges in the industry. In previous weeks, we’ve taken a closer look at financial asset graphs, data lineage, metadata management, fraud detection, anti-money laundering (AML) and network and IT infrastructure monitoring.
This week, we’ll take a closer look at identify and access management.
Graph Technology for Identity & Access Management
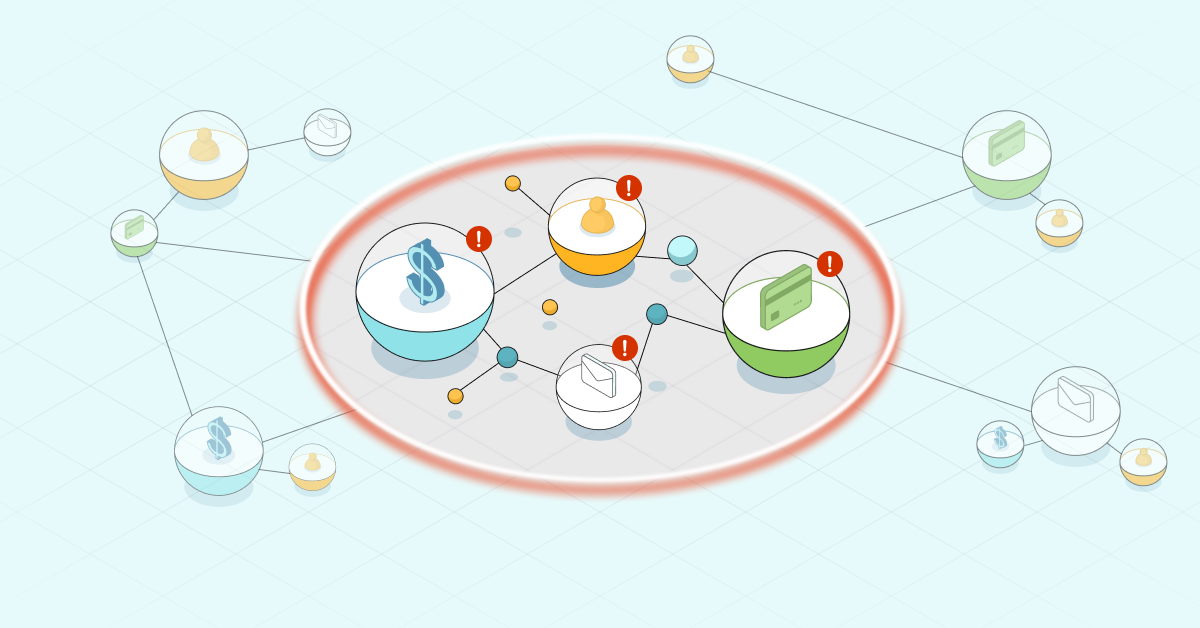
Because of the complexity of identity management infrastructure, administrators can’t easily determine who has what permissions. Users in one group may be granted permissions to assets they don’t necessarily need simply because that group belongs to another group that does need those permissions.
This “permissions creep” results in an increased risk of data breaches by both the insiders who are authorized to access it and by malicious outsiders who target privileged credentials to gain unauthorized access.
Corporate information security groups at financial services firms are using Neo4j to build identity and access management graphs to audit the entitlement structure and issue queries in real time to determine entitlements regardless of the complexity. With Neo4j, financial services firms are able to seamlessly track all identity and access authorizations and inheritances with substantial depth and real-time results.
The interconnected view of graph data produces better real-time insights and controls into entitlement access than custom-built directories. As a result, identity and access management happens quickly and effectively without complex, hours-long queries into the database.
Case Study: Global 500 Financial Services Company
When building a cross-asset investment banking platform, one Global 500 financial services company ran into significant challenges with user entitlement and authorization access.
Both externally and internally, various levels of users required access to the platform for activities as diverse as portfolio management, equities trading and foreign currency exchange. For such a high-profile platform, the firm required a robust permissions management solution.
This Global 500 financial services firm uses Neo4j to manage user identity and access management for its investment banking platform for both firm employees and their clients. Using Neo4j, the firm can easily track which users have access to which assets, activities, decision-making tools and more, and queries can be run in real time as users are added, removed or audited for fraud prevention.
The flexibility of the graph data model allows the firm to add, modify or delete new roles, assets and access rights without disrupting the day-to-day operations of the database or the investment platform. The current database has over one million nodes and six million relationships, and the overall database size is growing by 20% per year with no performance challenges.
Conclusion
The unending task of robust identity and access management isn’t unique to financial services, but the sensitive nature of financial data means managing entitlements must be of the highest priority, especially when dealing with highly dynamic and connected data.
Using Neo4j, your IT organization can easily map out authorizations at the individual and group levels and track them all dynamically as users’ roles change within the company, creating an effective competitive advantage for your enterprise.
In the coming weeks, we’ll take a closer look at other graph technology use cases within the financial services industry, including master data management, cybersecurity and customer experience management.
Catch up with the rest of the financial services and Neo4j blog series: